CodeTogether Live On-Premises Installation Guide
Roll out CodeTogether internally and keep your source 100% behind your firewall. To use CodeTogether On-Premises, pull down and configure the CodeTogether On-Premises container. The container provides a full set of collaboration services, including tailored client plugins for the host IDEs.
Installing CodeTogether
Contact Customer Service to obtain your license and registry credentials.
Review documents relevant to your On-Premises plan and configuration:
- Single Sign-On (SSO) Support—Configuration steps and environment variables that must be configured in the container if using single sign-on integration.
- Multi-Server On-Premises Deployment—An overview of multi-server CodeTogether deployment if you selected this plan.
- CodeTogether Edge Server Technical Notes—Advanced configuration and troubleshooting steps, including how to configure load balancers and access log files.
Set up your container using your preferred deployment technology:
Download pre-configured plugins and extensions for your IDEs from your on-premises server. These will be automatically updated when you update CodeTogether.
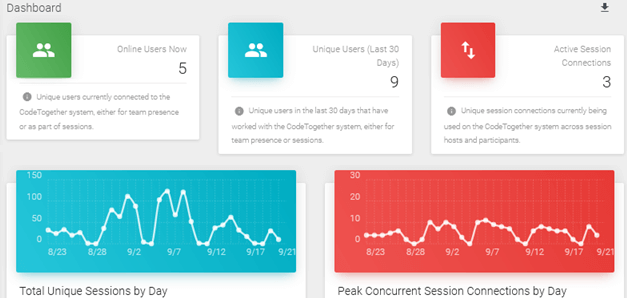
tipUse the metrics dashboard for access to real-time information and historical usage trends. Refer to Using the On-Premises Dashboard for more information.
Security
Due to security requirements, all communication in CodeTogether is required to be done via TLS, in addition to end-to-end encryption at the application layer. Besides strictly following secure coding practices, every CodeTogether Live build scanned using vulnerability checking tools like Snyk and Trivy. Penetration tests are frequently run on our container, ensuring that it is not susceptible to vulnerabilities and attacks. We build on the Red Hat UBI minimal image and our security audited listing can be found in the Red Hat Software Catalog.
Additional Resources
If you have any questions, email support@codetogether.com or contact your CodeTogether Sales representative.
For answers to common questions, refer to the On-Premises FAQ.